
PowerShell is more than a “Windows shell”. It’s an automation platform built around objects, remote management, and scripting best practices. In this guide you’ll learn the fundamentals, safe scripting patterns, and real-world automation examples for servers and hosting.
PowerShell is used heavily on a Windows VPS, but PowerShell 7 also runs on Linux — useful when you operate a mixed stack with a Linux VPS. All of this becomes especially valuable in production on stable VPS hosting, where automation prevents downtime and human error.
Automation is not about “cool scripts”. It’s about repeatability, auditability, and speed. With PowerShell you can:
pwsh) is cross-platform (Windows/Linux/macOS) and actively developed.For many administrators, the best approach is: keep 5.1 for legacy Windows modules, and use PowerShell 7 for cross-platform automation and modern scripting.
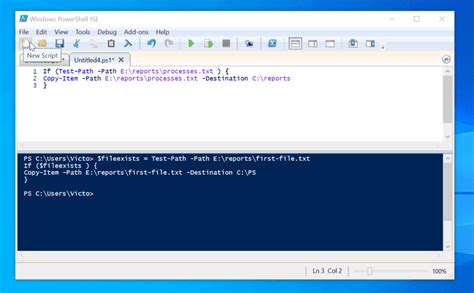
Execution policy is not a security boundary, but it prevents accidental execution of unsigned scripts. A common baseline for personal/admin scripts:
Set-ExecutionPolicy RemoteSigned -Scope CurrentUserTip: Use script signing and CI/CD for production automation where possible.
Get-Help Get-Process -Full
Get-Command *Firewall*
Get-Command -Module NetSecurityUnlike traditional shells that pass text, PowerShell passes objects. That means you can filter, sort, and export safely.
# Top CPU processes
Get-Process | Sort-Object CPU -Descending | Select-Object -First 10 Name, CPU, Id
# Export to CSV (reporting)
Get-Service | Select-Object Name, Status, StartType | Export-Csv C:Reportsservices.csv -NoTypeInformation
This pattern makes scripts predictable: parameters, strict mode, error handling, and clear output.
param(
[Parameter(Mandatory=$false)]
[string]$LogPath = "C:Logsautomation.log"
)
Set-StrictMode -Version Latest
$ErrorActionPreference = "Stop"
function Write-Log {
param([string]$Message)
$line = "$(Get-Date -Format s) `t $Message"
Add-Content -Path $LogPath -Value $line
Write-Host $line
}
try {
Write-Log "Script started"
# ... your logic here ...
Write-Log "Script completed successfully"
exit 0
}
catch {
Write-Log "ERROR: $($_.Exception.Message)"
exit 1
}# Enable RDP
Set-ItemProperty -Path 'HKLM:SystemCurrentControlSetControlTerminal Server' -Name 'fDenyTSConnections' -Value 0
Set-ItemProperty -Path 'HKLM:SystemCurrentControlSetControlTerminal ServerWinStationsRDP-Tcp' -Name 'UserAuthentication' -Value 1
# Enable built-in rules
Enable-NetFirewallRule -DisplayGroup 'Remote Desktop'
# Optional: restrict RDP to your IP (replace x.x.x.x)
New-NetFirewallRule -DisplayName "RDP (3389) - My IP only" -Direction Inbound -Protocol TCP -LocalPort 3389 -RemoteAddress x.x.x.x -Action AllowInstall-WindowsFeature -Name Web-Server -IncludeManagementTools
New-NetFirewallRule -DisplayName "HTTP (80)" -Direction Inbound -Protocol TCP -LocalPort 80 -Action Allow
New-NetFirewallRule -DisplayName "HTTPS (443)" -Direction Inbound -Protocol TCP -LocalPort 443 -Action Allow
# Local check
curl.exe -I http://127.0.0.1/$src = "C:ImportantData"
$dstDir = "D:Backups"
New-Item -ItemType Directory -Path $dstDir -Force | Out-Null
$zip = Join-Path $dstDir ("backup_{0}.zip" -f (Get-Date -Format "yyyy-MM-dd"))
Compress-Archive -Path (Join-Path $src "*") -DestinationPath $zip -Force
Write-Host "Backup created: $zip"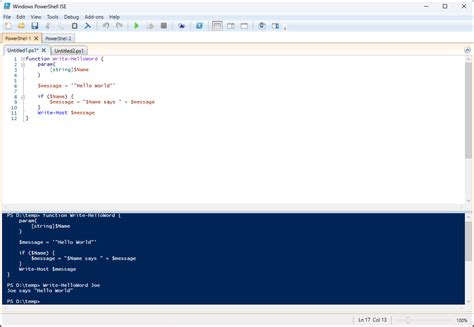
In Task Scheduler, run scripts with predictable flags:
powershell.exe -NoProfile -ExecutionPolicy Bypass -File "C:Scriptsbackup.ps1"Best practice: run scheduled tasks with least privilege, but enough rights to do the job. For server maintenance, SYSTEM is common, but document why.
PowerShell is a universal automation tool for IT professionals because it combines objects, scripting discipline, and deep OS integration. It’s essential on a Windows VPS, useful in mixed environments with a Linux VPS, and it becomes truly powerful at scale on reliable VPS hosting where repeatable automation saves time and prevents incidents.