Proper user management is one of the most important “production basics” for a Linux VPS. The goal is simple: avoid working as root, use role-based access, enforce strong authentication, and keep permissions predictable for teamwork and deployments.
This guide covers creating users, managing groups, issuing minimal sudo rights, password policies, SSH key access, shared directories (setgid/ACL), and a safe offboarding procedure. Start with a clean and stable Linux VPS to keep access control consistent from day one.
/etc/passwd (UID, GID, shell, home directory)./etc/shadow (root-only access)./etc/group (GID and members)./home/<user>, default skeleton: /etc/skel.Tip: most distributions use UIDs ≥ 1000 for human users, and smaller UIDs for system/service accounts.
sudo adduser alice
sudo usermod -aG sudo aliceVerify sudo rights (you’ll be asked for Alice’s password):
su - alice
sudo -v
sudo whoami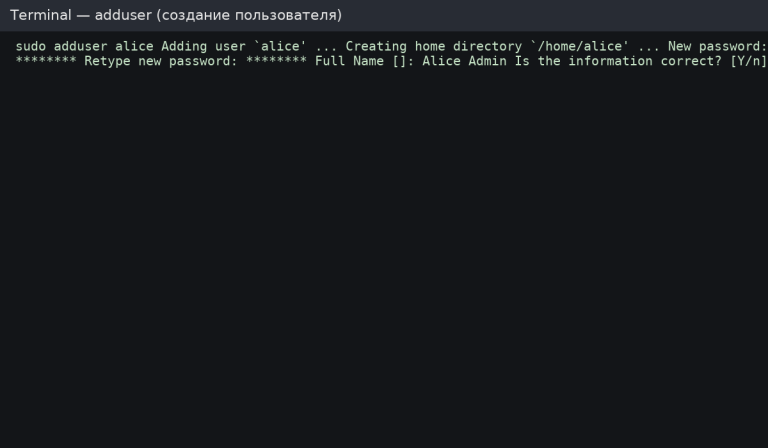
sudo useradd -m -s /bin/bash bob
sudo passwd bobUseful when you keep project users in /srv or a separate disk/volume.
sudo useradd -m -d /srv/users/charlie -s /bin/bash charlie
sudo passwd charlie
# Ensure strict permissions (example: only user + group can read)
sudo chown -R charlie:charlie /srv/users/charlie
sudo chmod 750 /srv/users/charlie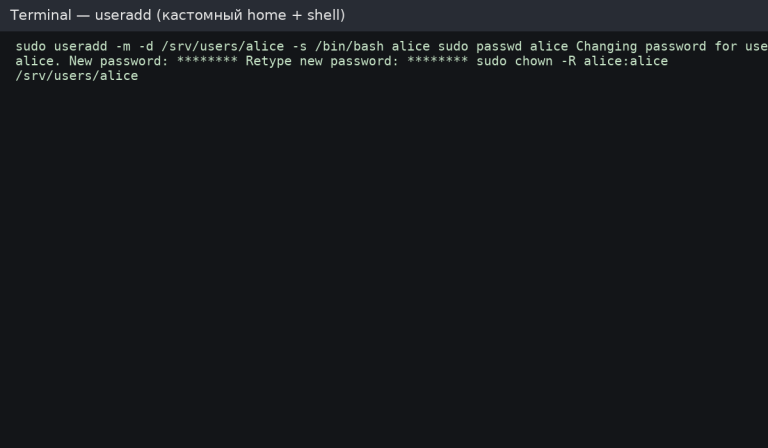
Verification:
id alice
getent passwd alice
ls -la /home/alice
sudo -l -U aliceGroups are the cleanest way to manage access. Avoid giving everyone “full sudo” — use role groups whenever possible.
# Add user to a group (example: docker)
sudo usermod -aG docker alice
# Show groups
groups alice
id alicesudo gpasswd -d alice dockersudo groupadd webadmins
sudo usermod -aG webadmins alice
sudo usermod -aG webadmins bobEdit sudo rules only via visudo — it validates syntax and prevents “bricking” admin access.
sudo visudoExample rule (do not duplicate if your distro already uses %sudo or %wheel):
%sudo ALL=(ALL:ALL) ALLCreate a dedicated sudoers file for the role group. Use absolute paths only.
sudo visudo -f /etc/sudoers.d/webadminsExample content:
# Allow only safe, specific commands (example)
%webadmins ALL=(root) NOPASSWD: /usr/sbin/nginx -t, /bin/systemctl reload nginx
# Recommendation: avoid NOPASSWD unless automation truly requires it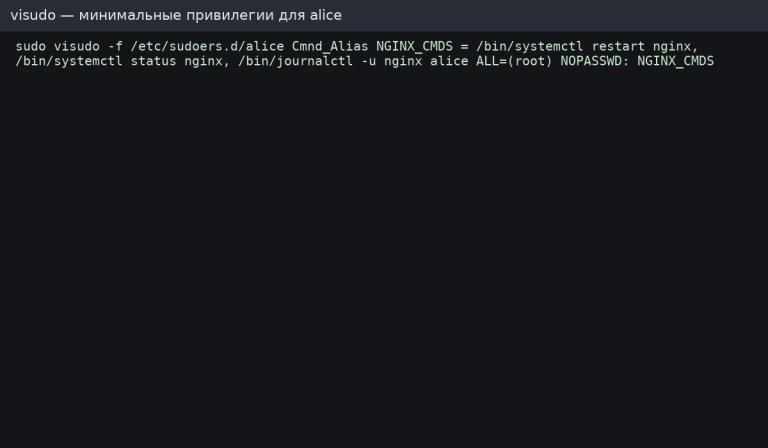
Best practice: grant permissions through groups whenever possible (%webadmins ...), then add/remove users from the group to manage access.
# Show current policy
sudo chage -l alice
# Example: max 90 days, min 1 day, warn 14 days before expiry
sudo chage -M 90 -m 1 -W 14 alicesudo nano /etc/login.defsExample baseline values:
PASS_MAX_DAYS 90
PASS_MIN_DAYS 1
PASS_WARN_AGE 14Install and configure password quality rules (test carefully on production systems).
sudo apt update
sudo apt install -y libpam-pwqualityEdit /etc/pam.d/common-password and add/adjust pam_pwquality parameters. Example:
password requisite pam_pwquality.so retry=3 minlen=14 ucredit=-1 lcredit=-1 dcredit=-1 ocredit=-1sudo -u alice mkdir -p /home/alice/.ssh
sudo -u alice chmod 700 /home/alice/.ssh
# Add the public key (replace with your actual key)
echo "ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAA... yourkey" | sudo tee -a /home/alice/.ssh/authorized_keys >/dev/null
sudo -u alice chmod 600 /home/alice/.ssh/authorized_keys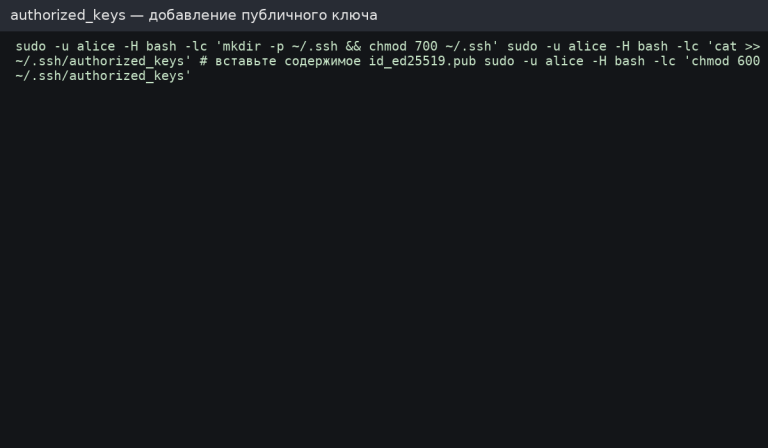
Hardening baseline: disable password auth, disable root login, and restrict SSH to a dedicated group.
sudo groupadd sshusers || true
sudo usermod -aG sshusers alice
sudo nano /etc/ssh/sshd_configExample directives:
PermitRootLogin no
PasswordAuthentication no
PubkeyAuthentication yes
AllowGroups sshusersReload SSH (Ubuntu/Debian):
sudo sshd -t
sudo systemctl reload sshCritical: verify key-based login works before disabling passwords, otherwise you may lose access.
Use a no-shell account for services and automation (reduces risk if credentials are exposed).
# Create a service user without interactive shell
sudo useradd -r -m -s /usr/sbin/nologin svcdeploy
# Lock password login (key-based only if needed)
sudo passwd -l svcdeployWith setgid, new files inherit the directory group automatically — very useful for team work.
sudo groupadd project || true
sudo mkdir -p /srv/project
sudo chown -R root:project /srv/project
# 2 in 2775 enables setgid bit
sudo chmod 2775 /srv/project
# Add users to the project group
sudo usermod -aG project alice
sudo usermod -aG project bobACL allows fine-grained permissions and default rules for newly created files.
sudo apt install -y acl || true
# Grant rwx to group on the directory (and set default ACL for new files)
sudo setfacl -m g:project:rwx /srv/project
sudo setfacl -d -m g:project:rwx /srv/project
# Check ACL
getfacl /srv/projectWhen multiple admins work on the same VPS, basic auditing helps track access and diagnose issues fast.
# Recent logins
last -a | head -n 20
# Last login per user
lastlog | head -n 20
# SSH logs (Ubuntu/Debian)
sudo tail -n 200 /var/log/auth.log
# Systemd-based view (often works everywhere)
sudo journalctl -u ssh --since "today" | tail -n 100 || true
sudo journalctl -u sshd --since "today" | tail -n 100 || trueA safe offboarding flow is: lock → stop sessions → backup → remove. This prevents surprises and preserves data when needed.
# 1) Lock password (prevents password auth)
sudo passwd -l alice
# 2) Disable shell (prevents interactive login if it’s still allowed)
sudo usermod -s /usr/sbin/nologin alice
# 3) Kill running processes (optional)
sudo pkill -u alice || true
# 4) Backup home directory (optional but recommended)
sudo tar -czf /root/alice-home-$(date +%F).tar.gz /home/alice
# 5) Remove user and home directory (final step)
sudo userdel -r alice/etc/sudoers.d with minimal privileges.chage/login.defs/PAM where needed).AllowGroups if used.Role-based access and clean user management make servers easier to operate and safer in production. Deploy a reliable Linux VPS, then set users, groups, sudo rules, and SSH access properly from day one.