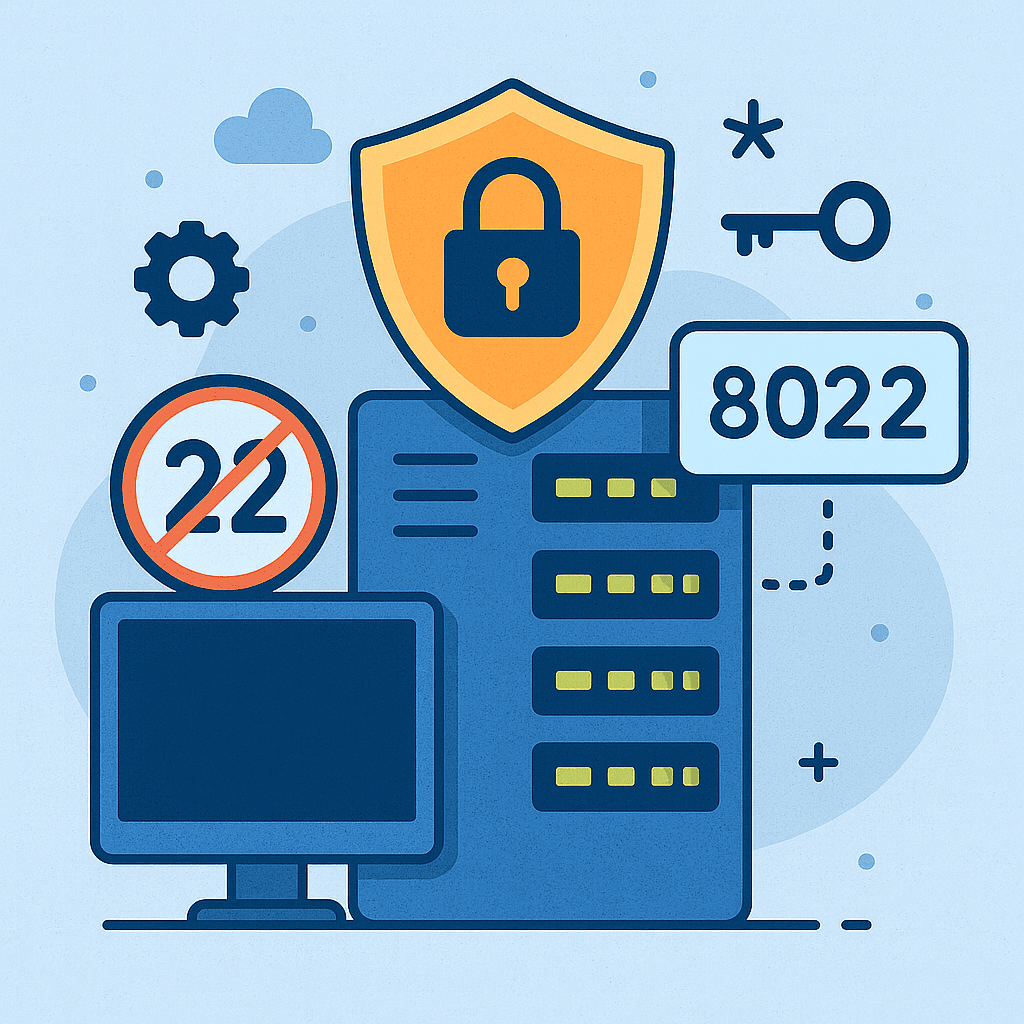
Changing default ports (like SSH 22 or RDP 3389) is a practical way to reduce automated scanning noise and brute-force attempts. It’s not “magic security”, but it’s a useful layer in a defense-in-depth strategy — especially on public VPS hosting.
This guide shows how to change ports safely on a Linux VPS (SSH) and on a Windows VPS (RDP), how to avoid lockouts, and how to validate firewall and connectivity.
Before changing any management port:
On a Linux VPS, SSH is usually the #1 target. The safest pattern is: allow new port → configure SSH → restart → test → then close old port.
Pick a port like 2222, 22022, or any high port that is not used by your services.
# Check if a port is already in use (replace 2222)
sudo ss -lntp | grep ':2222' || echo "Port 2222 is free"# Allow new SSH port
sudo ufw allow 2222/tcp
# Keep existing SSH port until you verify access
sudo ufw allow 22/tcp
sudo ufw statusIf you don’t use UFW, open the port in your firewall tool (iptables/nftables/firewalld) and also ensure it’s allowed in your VPS hosting provider panel firewall.
Edit SSH config:
sudo nano /etc/ssh/sshd_configSet (or add) these lines:
Port 2222
# Keep this enabled
PermitRootLogin no
PasswordAuthentication no
PubkeyAuthentication yesTip: It’s safer to first verify key-based login works, and only then disable passwords.
sudo sshd -t
sudo systemctl restart ssh
sudo systemctl status ssh --no-pager# From your local PC
ssh -p 2222 user@SERVER_IPOnly after you successfully login on the new port:
sudo ufw delete allow 22/tcp
sudo ufw statusOn a Windows VPS, changing the RDP port can reduce automated scans, but you should also restrict the rule by IP and keep NLA enabled. If possible, consider RD Gateway / VPN for external access.
Choose a port like 3390 or 53389. First open it in your provider firewall in the VPS hosting panel to avoid “it works internally but not externally”.
Run PowerShell as Administrator on the server (example uses 53389):
# Set new RDP port (Decimal)
$NewPort = 53389
Set-ItemProperty -Path 'HKLM:SystemCurrentControlSetControlTerminal ServerWinStationsRDP-Tcp' -Name 'PortNumber' -Value $NewPort# Allow inbound TCP on the new port
New-NetFirewallRule -DisplayName "RDP (TCP $NewPort)" -Direction Inbound -Protocol TCP -LocalPort $NewPort -Action AllowBest practice: restrict by your IP (replace x.x.x.x):
New-NetFirewallRule -DisplayName "RDP (TCP $NewPort) - My IP only" `
-Direction Inbound -Protocol TCP -LocalPort $NewPort -RemoteAddress x.x.x.x -Action AllowReboot is the simplest and most reliable way. If you cannot reboot immediately, restart the service (this can drop your current session):
Restart-Service TermService -ForceFrom Windows client:
Test-NetConnection SERVER_IP -Port 53389In mstsc, connect like: SERVER_IP:53389
ss/netstat checks).Changing a default port is a good “noise reduction” and hardening step, but the real security comes from strong authentication and restricted access. Use it as part of a layered approach on your Linux VPS or Windows VPS on professional VPS hosting.