Introduction
In today’s digital environment, threats to websites are growing every day. Even popular resources can fall victim to viruses, phishing attacks, or the injection of malicious code. At best, this leads to a loss of traffic or temporary blocking of access.
In the worst case, it can result in user data theft, sanctions from search engines, and reputational damage. Therefore, checking a website for malware is not just a one-time measure, but a regular practice that every administrator or owner of an online project should implement.
In this article, we will take a detailed look at how to recognize the symptoms of a website infection, what tools to use to detect viruses, how to respond in case of infection, and how to prevent similar incidents in the future.
Why websites get infected: hidden risks
A web resource can become infected for a variety of reasons. The most common are the use of outdated CMS versions or plugins, poorly secured feedback forms, and weak passwords for the admin panel or FTP access. Cybercriminals use automated scanners to find such vulnerabilities and quickly inject malicious scripts that then redirect users to phishing pages or attempt to infect their devices with viruses.
Sometimes the website owner is unaware of the infection for a long time because they do not see any external changes. But search engines quickly detect suspicious activity: the website loses its position in search results, browsers start blocking pages, and users leave the site.
How to check a website for malware: basic approaches
The first thing to do is to make sure that there is really something wrong with the website. Signs of infection may include:
- Unusual redirects to other resources;
- Browser warnings about danger when trying to open the site;
- Sudden decrease in traffic;
- Changes to site files that were not made by the administrator;
- User reports of extraneous elements or suspicious activity.
If you notice any of the above, it is worth checking.
Online checking tools
There are many free online services that allow you to analyze a website for malicious code:
- VirusTotal — one of the most popular services that checks URLs using dozens of antivirus systems.
- Google Safe Browsing — if a website is blacklisted, this tool will let you know.
- Sucuri SiteCheck — a free scanner that detects malware, viruses, blacklist status, and more.
- Quttera — in-depth analysis of website content, including scripts and potential threats.
These services not only show whether a website is infected, but also allow you to find out exactly where the dangerous code is located.
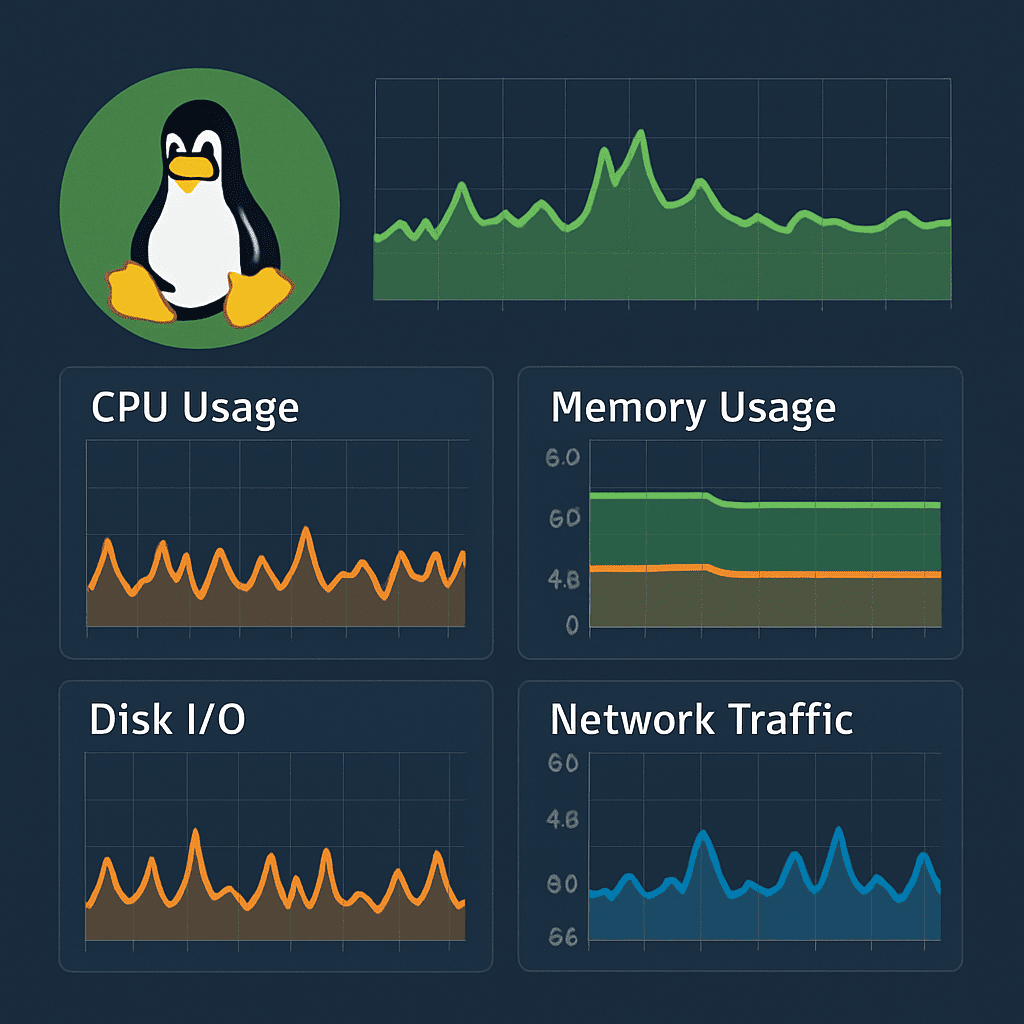
Hosting-level scanning
Many hosting providers, especially VPS and premium plans, offer automatic security systems. They can perform regular file scans, check for suspicious changes, and block malicious scripts before they are activated.
If you use a CMS such as WordPress, installing plugins such as Wordfence, iThemes Security, or Sucuri Security will help detect malicious code injections, changes to core files, and potential security holes.
What to do if your website is infected
Once you have confirmed an infection, don’t panic. You need to act clearly and consistently:
- Make a backup copy of your website. Even if it is infected, this will allow you to analyze the source code, roll back changes, or check for modifications.
- Isolate your website. Temporarily disable it or block access from the external internet.
- Analyze the log files. They may contain information about suspicious IP addresses, dates of infection, or paths of entry.
- Clean up the code. Remove malicious scripts manually or with plugins, check the .htaccess, index.php, functions.php files, etc.
- Update the CMS and all plugins. This is critical to close vulnerabilities.
- Change all passwords. For hosting, FTP, CMS admin, database.
- Notify search engines. Through Google Search Console or Yandex.Webmaster, you can submit a request for re-verification if your site has been blacklisted.
How to protect your site in the future
To avoid infections in the future, we recommend:
- Regularly update the platform and its components.
- Use complex passwords and two-factor authentication.
- Only install plugins and templates from official sources.
- Regularly scan your website and check the logs.
- Use a VPS with built-in cybersecurity tools.
Conclusion
Checking your website for malware is not difficult, but it is very important. Timely diagnosis, thorough scanning with online tools, and monitoring by your hosting provider can save your reputation, traffic, and customer trust. Don’t put off protecting your website: make security a priority today.